In today's interconnected digital world, the need for robust cloud security solutions has never been greater. From protecting sensitive data to safeguarding critical applications, the realm of cloud security solutions plays a pivotal role in ensuring the integrity of online operations.
This article delves into the intricacies of cloud security solutions, shedding light on their importance, types, implementation strategies, challenges, and future trends. Let's unravel the complexities of cloud security solutions together.
Overview of Cloud Security Solutions
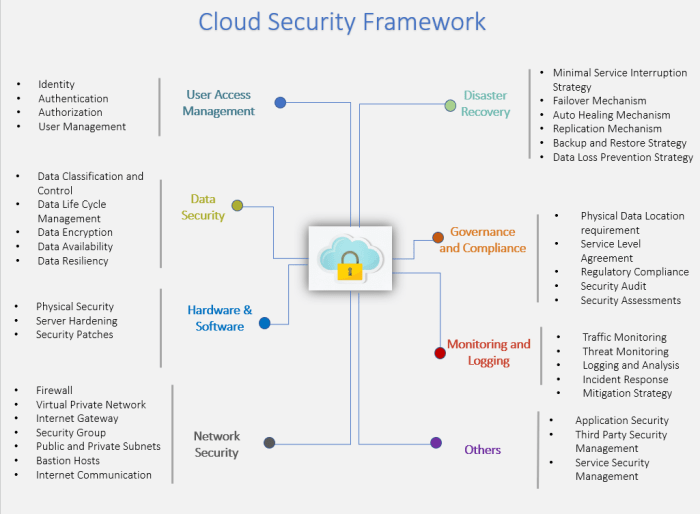
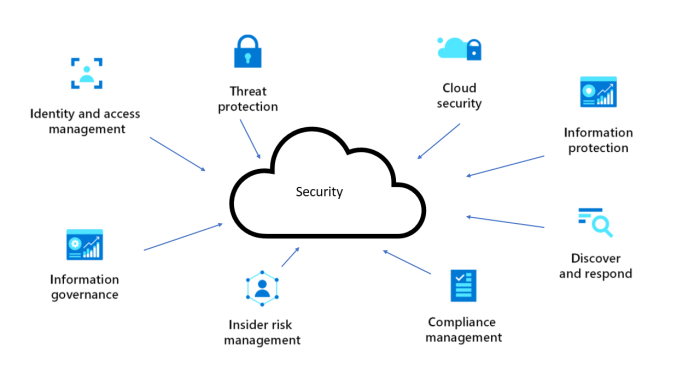
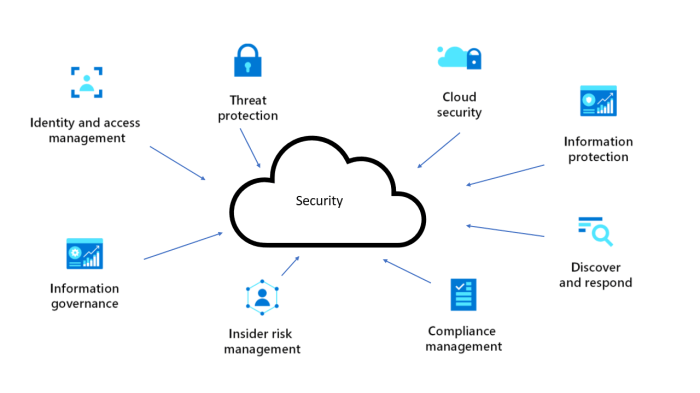
Cloud security solutions refer to a set of tools, technologies, and practices designed to protect data, applications, and infrastructure in cloud environments. In today's digital landscape, where organizations increasingly rely on cloud services to store and process sensitive information, ensuring the security of these assets is paramount.
Role of Cloud Security Solutions
Cloud security solutions play a crucial role in safeguarding data and applications stored in the cloud from unauthorized access, data breaches, and other cyber threats. By implementing robust security measures, organizations can mitigate risks and ensure the confidentiality, integrity, and availability of their cloud-based resources.
- Encryption: Cloud security solutions often employ encryption techniques to protect data both at rest and in transit, ensuring that information remains secure even if it is intercepted.
- Access Control: These solutions enable organizations to control who has access to their cloud resources and establish permissions based on roles and responsibilities.
- Monitoring and Incident Response: Cloud security solutions provide tools for monitoring cloud environments for suspicious activities and responding promptly to security incidents.
- Compliance Management: Organizations can use cloud security solutions to ensure compliance with industry regulations and standards, minimizing the risk of penalties and legal consequences.
Types of Cloud Security Solutions
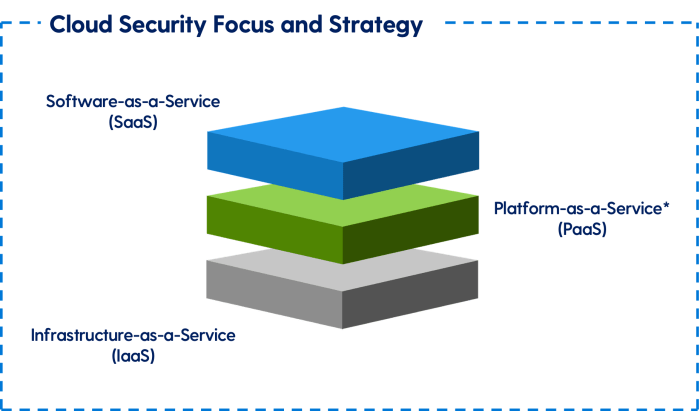
When it comes to securing cloud environments, there are various types of cloud security solutions available in the market. Each type serves a specific purpose in ensuring the confidentiality, integrity, and availability of data stored in the cloud.
Encryption
Encryption is a fundamental cloud security solution that involves encoding data to make it unreadable to unauthorized users. This ensures that even if data is intercepted, it cannot be deciphered without the encryption key.
Example: Using AES encryption to protect sensitive data stored in the cloud, ensuring that only authorized users with the decryption key can access it.
Access Control
Access control mechanisms help in managing user permissions and restricting access to sensitive data in the cloud. This ensures that only authorized users can view, modify, or delete data based on their roles and responsibilities.
Example: Implementing role-based access control (RBAC) to assign specific permissions to users, limiting their access to relevant data and resources in the cloud.
Intrusion Detection
Intrusion detection systems (IDS) are used to monitor cloud environments for suspicious activities or potential security breaches. They analyze network traffic and system logs to identify and respond to unauthorized access attempts in real-time.
Example: Deploying an IDS that detects and alerts administrators of any unusual network behavior or unauthorized access to cloud resources, enabling prompt action to mitigate security threats.
Implementation of Cloud Security Solutions
Implementing cloud security solutions is crucial for organizations to protect their data and applications in the cloud. It involves following a series of steps and best practices to ensure a seamless integration into existing IT infrastructure.
Steps for Implementing Cloud Security Solutions
- Evaluate Current Security Measures: Assess existing security protocols and identify potential vulnerabilities.
- Choose Appropriate Cloud Security Solutions: Select solutions that align with the organization's security requirements and budget.
- Deploy Security Controls: Implement encryption, access controls, and monitoring tools to protect data and applications.
- Train Employees: Provide training on best practices for using cloud security solutions effectively.
- Regularly Update and Test: Keep security solutions up to date and conduct regular security testing to identify and address any weaknesses.
Best Practices for Integrating Cloud Security Solutions
- Understand Compliance Requirements: Ensure that cloud security solutions comply with industry regulations and standards.
- Collaborate with IT and Security Teams: Involve IT and security teams in the decision-making process to ensure a comprehensive approach to security.
- Implement Multi-Factor Authentication: Enhance security by requiring multiple forms of verification for access to sensitive data.
- Monitor and Analyze Security Events: Utilize security analytics tools to detect and respond to security incidents in real-time.
Ensuring Seamless Adoption and Deployment
- Start with a Pilot Project: Test cloud security solutions on a small scale before full deployment to identify any issues.
- Communicate with Stakeholders: Keep all stakeholders informed about the implementation process and address any concerns they may have.
- Provide Ongoing Support: Offer training and support to employees to ensure they understand how to use cloud security solutions effectively.
- Regularly Assess and Improve: Continuously evaluate the effectiveness of cloud security solutions and make adjustments as needed to enhance security posture.
Challenges in Cloud Security Solutions

When organizations implement cloud security solutions, they often face various challenges that can impact the effectiveness of their security measures. These challenges range from compliance issues to security vulnerabilities that need to be addressed promptly to ensure the safety of data and systems.
Compliance Issues in Cloud Security
One of the primary challenges faced by organizations in implementing cloud security solutions is ensuring compliance with regulations and industry standards. Many industries have strict guidelines regarding data protection and privacy, and failure to comply can result in severe consequences such as fines or legal actions.
It is essential for companies to stay updated on the latest regulations and ensure that their cloud security measures align with these requirements to avoid compliance issues.
Strategies for Overcoming Security Gaps
Another common challenge is addressing security gaps and vulnerabilities in cloud environments. With the increasing sophistication of cyber threats, organizations need to constantly update their security measures to stay ahead of potential risks.
- Regular security audits and assessments can help identify vulnerabilities and gaps in the cloud infrastructure.
- Implementing multi-factor authentication and encryption techniques can enhance data protection in the cloud.
- Training employees on best practices for data security and privacy can help prevent security breaches caused by human error.
- Collaborating with cybersecurity experts and investing in advanced threat detection tools can strengthen overall security posture.
Future Trends in Cloud Security Solutions
![What Is Cloud Security? [2024 Updated Guide] What Is Cloud Security? [2024 Updated Guide]](https://cloud.hops.id/wp-content/uploads/2026/04/Types-of-Cloud-Security-1.png)
The landscape of cloud security solutions is constantly evolving to keep up with emerging threats and technologies. Let's explore some of the key trends shaping the future of cloud security.
AI-driven Security Measures
AI-driven security measures are expected to play a crucial role in enhancing cloud security. By leveraging artificial intelligence and machine learning algorithms, organizations can automate threat detection and response processes, enabling faster and more effective incident response. AI can analyze vast amounts of data in real-time to identify patterns and anomalies that may indicate a security breach, helping organizations stay one step ahead of cyber threats.
Impact of Blockchain on Cloud Security
Blockchain technology has the potential to revolutionize cloud security by providing a decentralized and tamper-proof way to store and verify data. By using blockchain to secure sensitive information and transactions in the cloud, organizations can reduce the risk of data manipulation and unauthorized access.
Blockchain can also enhance the integrity and transparency of data stored in the cloud, making it easier to track changes and verify the authenticity of information.
Evolution of Cloud Security Solutions
Cloud security solutions are evolving to meet the changing threat landscape, with a focus on proactive security measures and threat intelligence. Organizations are increasingly adopting a holistic approach to cloud security, combining technologies such as encryption, multi-factor authentication, and security analytics to protect their data and applications.
As cybersecurity threats continue to advance, cloud security solutions will need to adapt and innovate to stay ahead of cybercriminals.
Last Recap
As we conclude our exploration of cloud security solutions, it becomes evident that the landscape of digital security is constantly evolving. By staying abreast of emerging trends and implementing best practices, organizations can fortify their defenses and mitigate potential risks in the ever-changing cyber realm.
Embracing innovation and proactive security measures is key to ensuring a secure digital future for all.
General Inquiries
What are some common types of cloud security solutions?
Some common types include encryption, access control, and intrusion detection systems.
How can organizations ensure seamless adoption of cloud security solutions?
By following best practices, conducting thorough assessments, and integrating solutions into existing IT infrastructure gradually.
What are the future trends in cloud security solutions?
Upcoming trends may include AI-driven security measures and the impact of technologies like blockchain on cloud security.